
Creating the Telegram messenger, the development team led by the Durov brothers focused on protecting users' personal data and confidentiality of correspondence.
The increased level of security has become the main feature of Telegram, which favorably distinguishes it from the background of other instant messengers. Thanks to this, Telegram gained popularity, after all, many Internet users install this messenger, making a choice in favor of maintaining anonymity, security and privacy of personal correspondence. But along with the popularity of Telegram, it also gained detractors. On the Internet, you can often find devastating articles and holivars on forums that security in Telegram is imaginary, and all the features, such as secret chats and encrypted calls, are just a PR from Pavel Durov.
In this article we will try to understand the security principles of Telegram and find out how secure this messenger is and what the likelihood is that attackers will be able to intercept and read users' personal correspondence.
- How Works Security in Telegram
- Attempts to Hack Telegram
- Telegram and Relations With The Governments of Some Countries
How Works Security in Telegram

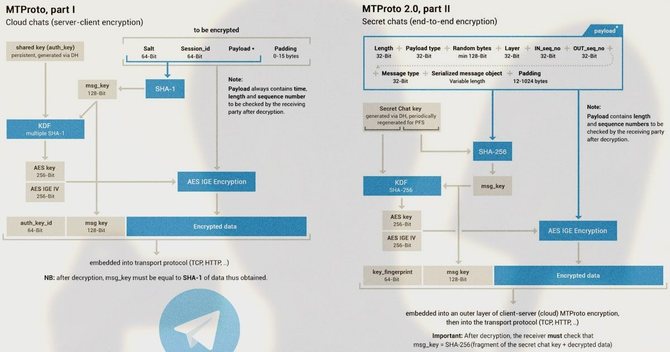
In short, security in Telegram is based on the MTProto Proxy cryptographic protocol. The features of this protocol are as follows:
- Using a secret key instead of the standard "login + password" link (the key is created at the time of the client's registration and is securely encrypted);
- Using two types of encryption: client-server (for regular messaging) and client-client (for secret chats);
- Traffic transmission through Telegram channels is disguised as a standard TSL / SSL connection, but inside the data is encrypted in such a way that nothing can be recognized;
- MTProto Proxy is a special type of proxy designed specifically for the Telegram messenger, which means that other applications do not work on it, and regular Internet traffic cannot be transmitted through this protocol.
You can read more about how MTProto Proxy works in our article.
Encryption

As we mentioned above, Telegram uses two types of encryption: "client-server" and "client-client". Let's take a closer look at what their purpose and their differences are.
Client-server
Most messengers use the most common type of client-server encryption. It works like this: Dan sends a message to Nate via a messenger. A message from Dan in encrypted form is sent to the messenger's server, the server decrypts it, after which it encrypts it again and sends it to Nate.
That is, messages on the way from Dmitry's device to the server and from the server to Natalya's device are safely protected from interception. But if a successful attack is made on the server, then all unencrypted information can fall into the hands of attackers.
Client-client
This type of encryption is called end-to-end, since data transmission from the sender's device to the user's device is transmitted "through" the server. That is, they are transmitted through the server, but the server itself cannot decrypt this data, because encryption keys are located only on users' devices, and the data itself is stored on the server in encrypted form.
This type of encryption ensures that all messages, calls, audio files, videos, images, documents and other data are protected from falling into third hands — they are available only to users of correspondence and are the most secure. This type of encryption is used by Telegram in secret chats.

Next, we will look at how a user can increase the security level in the Telegram messenger.
Secret Chats

So, if a user wants to send extremely confidential information to another user, then he should use the secret Telegram chat.
No one can intercept and decrypt the message, not even the developers. This method is considered the safest in Telegram.
In this case, in the secret chat it is possible to set a timer for the automatic destruction of messages with a range. Also in the secret chat there is no possibility to forward the message to a third party —the forwarding option is disabled here. And if the user tries to take a screenshot of the correspondence, the interlocutor will receive a notification about this.

But keep in mind that you are not insured in cases where an attacker can take a picture of the screen of the device on which the correspondence is displayed.
Cloud Password
Each time entering Telegram from a new device, the application will require the user to enter a one-time confirmation code that comes to the user's phone in the form of an SMS message or a notification in Telegram.
But if the attacker has the ability to intercept the user's SMS messages, then this protection method will not help much. Therefore, it is recommended to use two-step authentication, commonly referred to as a cloud password. This will significantly increase security in Telegram.

By setting a cloud password, login Telegram from a new device will become more secure, since in addition to a one-time confirmation code, you will have to enter a single additional password, which is known only to the owner of the Telegram account. Also, if third parties try to change this password, a notification will be sent to the user's email address that the password has been changed, thereby reporting suspicious activities with his account.
You can read about how to correctly set up a cloud password in this article: Cloud Telegram Password: How to Set Up, Install and Use
Passcode
The developers also took care of making it more difficult for attackers to access the user's correspondence if the device fell into their hands. By setting a passcode, access to chats will be blocked. The passcode can be set as a PIN or regular password. But it can be easily reset by reinstalling the app on the device.
Therefore, it is highly recommended to use the cloud password option, which will prevent an attacker from logging into the Telegram user account.
A password code is very convenient for protecting correspondence from the prying eyes of colleagues or household members. So the presence of a password code will not be an unnecessary security measure in Telegram.
To set a passcode, you need to follow the steps of the following sequence:
- Login the Telegram side menu and open the "Settings" section;
- Go to the "Privacy" section and scroll down to the "Security" subsection;

- Click on the "Passcode" option, that is, move the slider to the right;
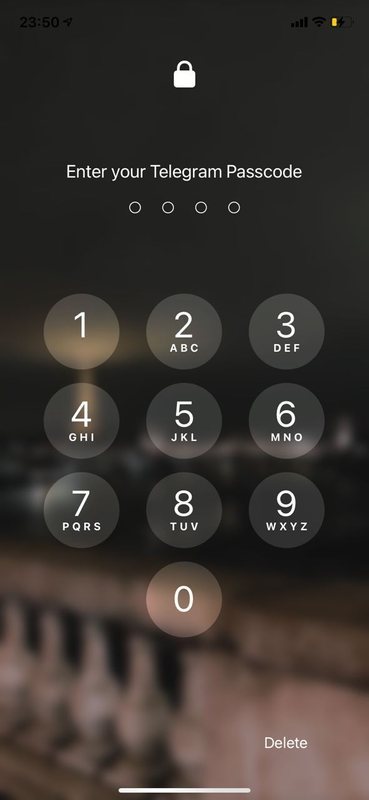
- A dialog window will open asking you to enter your password;
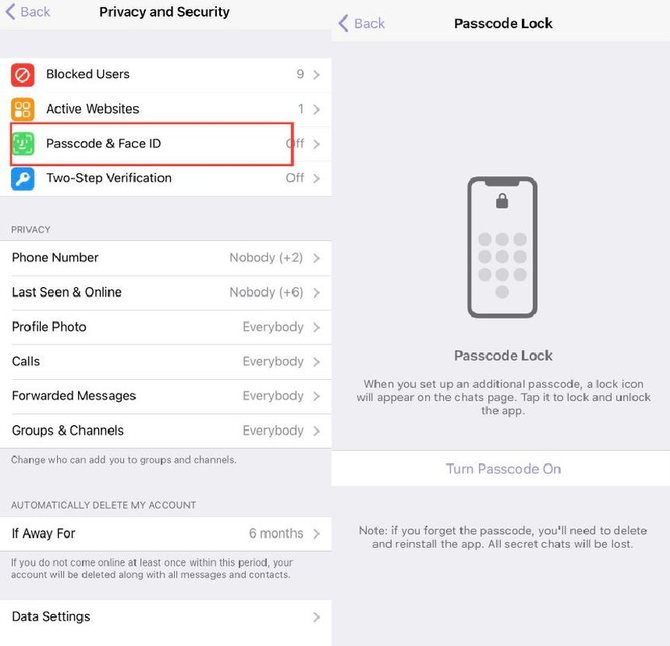
- At the top there will be an option with a choice of the type of password: PIN-code or regular password, choosing one of them, you need to enter characters (in the case of a PIN-code, these are four numeric characters, in the case of a regular password - any characters, including letters, numbers and punctuation marks);
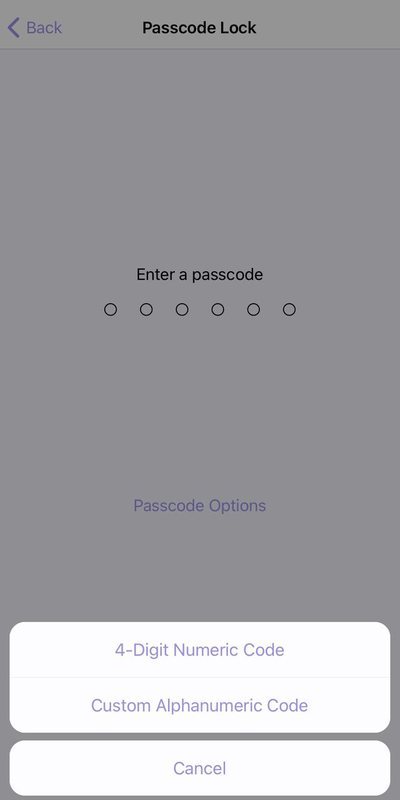
- After setting the password, a lock icon will appear in the header above the chat list;
- The next time you unlock your phone and try to enter Telegram, the application will ask you to enter a password code.
Setting up a passcode on iOS and Android gadgets is identical. For the desktop version of Telegram, this setting algorithm is also suitable.
Setting Phone Number Visibility
It is known that the user's Telegram account is attached to his phone number. Therefore, the user can easily be found in Telegram, knowing his number. But the developers took care here too: they introduced the ability to adjust the visibility of a phone number in such a way that the user himself chooses whom to show the phone number and to whom not.
To configure this option, the user needs to go to Settings / Privacy / Phone number and put the necessary restrictions there. In these settings, you can both prevent everyone from seeing the phone number, and make exceptions for certain users.

Showing Last Activity
Also, one of the security principles in Telegram is hiding information about user activity in the messenger. Any user can see the last time another user logged into Telegram. Therefore, the developers added the "Last Activity" option, in which the user can customize the display of this information.
In case of hiding activity from everyone, information about the last user login will be displayed approximately. For example, “recently” can mean a period from 1 minute to 1 day, and “was long ago” can mean 1 week or longer. This option can be configured by following these steps: Settings / Privacy / Last Activity.
You can also read about other useful functions of the messenger in the article on Telegram chips.
Attempts to Hack Telegram

Hacking Telegram is one of the most popular trends in recent years. On the network, you can find articles about how someone was hacked somewhere, took control of groups and channels, but there is no confirmation from official authoritative sources about such cases. And usually Telegram channels and groups are "taken away" because of the carelessness of the owners, who neglect the elementary Telegram security rules.
Many victims of these cases did not use 2-Step Verification.
Sometimes you can come across criticism of Telegram from reputable publications that specialize in information security. The criticism mainly concerns the fact that the Telegram company does not fully disclose the source code of the messenger. They also criticize the fact that Telegram developers use modifications of standard protocols for encryption, which can lead to unpredictable consequences.
Nevertheless, Pavel Durov is confident in the safety of Telegram. He announced a couple of times a contest for hacking Telegram. As a reward, he once offered $ 200,000 in bitcoins, and another time — $ 300,000. But no one managed to get a reward, as no winners were identified.
Below we will consider several known attempts to hack Telegram.
Disable SMS Service

Pavel Durov stated that there were a couple of cases when the Russian special services tried to get access to the Telegram accounts of some oppositionists and journalists. The first case occurred in 2016 with activist Oleg Kozlovsky and employee of the Anti-Corruption Foundation Georgy Alburov.
They complained that their account in the Telegram messenger had been hacked, and the reception of SMS messages had been disabled. Oleg Kozlovsky himself figured out this situation and came to this conclusion, that the MTS company purposefully disabled the message delivery service for him. When the attackers logged into his account from another device, he did not receive an SMS notification with an authorization code.
In his Telegram account, he received a notification that the account was accessed from a specific device (the notification indicates the IP address and the device), but he saw this notification only in the morning. It is noteworthy that in a few minutes Georgy Alburov's account was logged in from the same IP address. A few hours later, MTS turned on the SMS delivery service again. Kozlovsky turned to MTS technical support with a request to find out why the delivery service was disabled for him, but in response he received a refusal and a recommendation to make a written request.
As a result, Kozlovsky suggested that the attackers could get access to the code from SMS either through the SORM system or through the technical security department of MTS. Later, Durov, in conversation with the editor of the radio station "Echo of Moscow", commented on this case, suggesting that the special services are putting pressure on mobile operators. And recommended using two-step authentication, which we wrote about above.
The second known case occurred in 2019. The attempted break-in was reported by several journalists who covered the protests in Ekaterinburg over the construction of the church. Fortunately, their accounts were not hacked as they had 2-Step Verification configured. But they received notifications about an attempt to log in from another device. Durov also commented on this situation in his official Telegram channel. He wrote that the authorities unsuccessfully tried to hack the Telegram accounts of journalists and drew attention to the fact that the authorities of authoritarian countries infringe on the privacy and security of citizens.
Phishing

Phishing is one of the ways to gain unauthorized control over a Telegram user account. In the case of phishing, the user receives a notification in the Telegram messenger from an account masquerading as the official Telegram support account.
This notification provides information that suspicious activity has allegedly been detected in the user's account and he must immediately confirm his actions, otherwise his account will be blocked.
For confirmation in the notification, the attackers include a link to a fake page that visually completely copies the official Telegram website. Like telegram-antispam.org. On a fake site, the user will have to indicate the mobile phone number attached to the Telegram account, the confirmation code and the cloud password, if enabled. If the user has forgotten the password, the scammers ask the account owner to go through the standard password recovery process. As soon as the deceived user enters all of the above information, the attackers gain full control over the Telegram account.
They link the stolen account to a different phone number and gain full access to the user's chats, group and channels. Especially at risk are those users who run their own telegram channels. They are usually a tidbit for attackers, as they in turn can monetize stolen channels or use them for more nefarious purposes.

To avoid becoming a victim of phishing, the t9gram editors recommend that users adhere to several rules:
- Always use 2-Step Verification;
- Be vigilant when receiving messages from accounts that are not in the contact list (official Telegram accounts have confirmation icons in the form of gears or checkmarks);
- If the user nevertheless followed the link to the fake site, then he must make sure that the connection is protected, and the correct telegram.org address is indicated in the address bar of the site.
Spyware On The Device
Attackers can also gain access to the Telegram account by installing spyware on the user's device. For example, like FinSpy and Skygofree. Unfortunately, 2-Step Verification here won't help you protect your data. Therefore, the user should be vigilant about what software or application he installs on his smartphone or PC and make sure that good anti-virus programs are installed on its devices, then your Telegram will be safe.
Telegram and Relations With The Governments of Some Countries
At the beginning of the article, we mentioned that the Telegram management values the users' right to confidentiality of correspondence and believes that that the government and intelligence agencies should not interfere with the private life of citizens. Nevertheless, the Telegram company in 2018 announced that it was changing the privacy policy of the messenger and was ready to provide information about users to special services. But only on legal grounds, that is, if there is a court order that confirms that a certain user is suspected of terrorism, the company's management is ready to provide the special services with the user's mobile phone number and IP-address. But the conversation will remain confidential.
At the same time, a special channel was opened in Telegram, in which information on cooperation with special services will be published. To date, there is no information about such cases of cooperation, the mentioned channel is empty.
Blocking in Iran
In the Islamic Republic of Iran, the Telegram messenger was blocked due to the fact that in one of the groups the administrator urged users to participate in protests against the government using Molotov cocktails. This happened at the end of 2017. The Iranian government via Twitter asked Pavel Durov to ban the group with the protesters, Durov complied with the request and noted that criticism in public channels and Telegram groups is acceptable, but calls for violence are not. But the administrators of the banned group created a new group and wrote to Durov that they had fired the aggressive administrator who was calling for violence. Durov was satisfied with this answer and the group avoided another ban, but the Iranian government remained dissatisfied.

The existence of the opposition group became a formal reason for blocking Telegrams in the country. Partially Telegram on the territory of Iran has been blocked since the end of 2017, and completely since April 2018.
Conflict with Roskomnadzor
Telegram also did not escape the conflict with the government of the Russian Federation, or rather with Roskomnadzor. As a result of the adoption of the Yarovaya law, all telecommunications companies were required to closely cooperate with the special services, that is, at the very first request of the special services, provide information about "suspicious" users.
And in this situation, Durov again did not betray his principles. The stumbling block was Durov's unwillingness to provide Roskomnadzor with encryption keys that would give access to the user's correspondence. At the same time, Durov correctly explained that in the case of using end-to-end encryption, this is technically impossible, but Roskomnadzor insisted on its own. In the end, this resulted in lawsuits and led to the "clumsy" blocking Telegram in Russia.

Fortunately, to date, the conflict with Roskomnadzor has been settled and unhindered access to the Telegram messenger on the territory of the Russian Federation is slowly being restored.
De-anonymizing Protesters in Hong Kong

In the People's Republic of China, Telegram is also blocked. And this is done due to the fact that with the help of the messenger, the opposition coordinates its attacks against the communist government of the country. The fact that Telegram has fallen out of favor with the Chinese government is not surprising. In China, the authorities require all telecommunications companies to install their servers in the country and give special services access to users' conversations. Durov did not agree to this.
The principles of libertarianism are paramount. By the way, you can read the biography of Pavel Durov in this article. Nevertheless, Telegram is partially blocked in China, for example, in Hong Kong and Macau, the messenger is functioning normally.
But in 2019, an unpleasant event happened. In Hong Kong, protests began in the summer against the government in connection with the extradition law. The protesters coordinated their actions through group chats on Telegram. At some time, the special services began to identify the identity of the protesters and suspicion fell on Telegram — allegedly, the messenger team gave information about them to the special services. In fact, this is not the case, security in Telegram has not changed.
It was mentioned above that the user himself can configure the privacy level in Telegram. In the case of hiding a phone number, the user can hide his phone number from everyone. BUT there is one nuance.
Even if the user has chosen the option to hide the phone from everyone, then people whose phone number is entered in the contact list will still see his number in Telegram. It was with the help of this loophole that the special services calculated the identity of the protesters.

An attacker (in this case, a hacker hired by the Chinese authorities) enters tens of thousands of phone numbers into his contact list. Then he goes to Telegram, synchronizes contacts and joins target groups, where protesters coordinate their movements. After that, the attacker opens the list of contacts in Telegram, clicks on the user's contact and sees what groups he has with him, that is, he sees if Yoon Li is in the same protest group as the attacker. Thus, deanonymization in Telegram took place.
You can protect yourself from this method of deanonymization only if the user has issued his SIM card to a dummy. Perhaps the Telegram developers should in the future come up with a way to protect against deanonymization and remove this loophole. This is the most serious security vulnerability in Telegram to date.
In general, the Telegram messenger is equipped with a high level of security and gives the user the choice to decide for himself how much he wants to be protected. And nevertheless, no matter how much the developers supply the messenger with additional security chips, the user must remember that the level of security depends primarily on his own vigilance.
How to Hide a Number in Telegram
How to Write to Yourself in Telegram: iOS, Android and Computer
How to Add a Contact to Telegram by Phone Number or Nickname